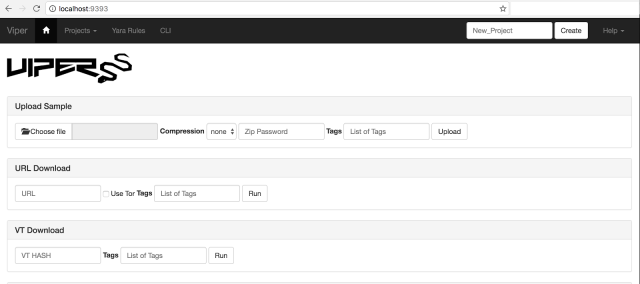
Source: https://github.com/viper-framework/viper
Goal: Install a malware repository box for subsequent storage and malware triage to Cuckoo.
Steps: python viper-web
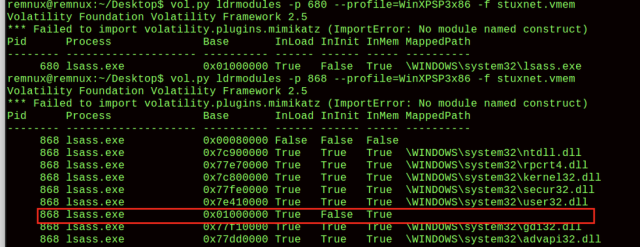
[*] Session opened
[*] DLL: MSVCRT.dll
– 0x43e0e0: memset
– 0x43e0e4: wcsstr
– 0x43e0e8: malloc
– 0x43e0ec: free
– 0x43e0f0: wcslen
– 0x43e0f4: wcscpy
– 0x43e0f8: wcscat
– 0x43e0fc: memcmp
– 0x43e100: _strdup
– 0x43e104: sprintf
– 0x43e108: atoi
– 0x43e10c: strlen
– 0x43e110: strstr
– 0x43e114: _strnicmp
– 0x43e118: strncpy
– 0x43e11c: strcmp
– 0x43e120: sscanf
– 0x43e124: strcpy
– 0x43e128: memcpy
– 0x43e12c: _wcsicmp
– 0x43e130: wcsncpy
– 0x43e134: localtime
– 0x43e138: mktime
[*] DLL: KERNEL32.dll
– 0x43e140: GetModuleHandleW
– 0x43e144: HeapCreate
– 0x43e148: GetProcAddress
– 0x43e14c: HeapDestroy
– 0x43e150: ExitProcess
– 0x43e154: LoadLibraryW
– 0x43e158: Sleep
– 0x43e15c: HeapFree
– 0x43e160: CloseHandle
– 0x43e164: InitializeCriticalSection
– 0x43e168: GetEnvironmentVariableW
– 0x43e16c: SetEnvironmentVariableW
– 0x43e170: GetCurrentProcess
– 0x43e174: DuplicateHandle
– 0x43e178: CreatePipe
– 0x43e17c: GetStdHandle
– 0x43e180: HeapAlloc
– 0x43e184: CreateProcessW
– 0x43e188: WaitForSingleObject
– 0x43e18c: EnterCriticalSection
– 0x43e190: LeaveCriticalSection
– 0x43e194: MultiByteToWideChar
– 0x43e198: FreeLibrary
– 0x43e19c: CreateFileW
– 0x43e1a0: WriteFile
– 0x43e1a4: LoadLibraryA
– 0x43e1a8: GetDriveTypeW
– 0x43e1ac: FindFirstFileW
– 0x43e1b0: FindClose
– 0x43e1b4: GetFileAttributesW
– 0x43e1b8: GetTempPathW
– 0x43e1bc: SetFileAttributesW
– 0x43e1c0: DeleteFileW
– 0x43e1c4: GetLocalTime
– 0x43e1c8: HeapReAlloc
– 0x43e1cc: DeleteCriticalSection
– 0x43e1d0: AllocConsole
– 0x43e1d4: GetConsoleScreenBufferInfo
– 0x43e1d8: SetConsoleCtrlHandler
– 0x43e1dc: SetConsoleTitleW
– 0x43e1e0: WideCharToMultiByte
[*] DLL: USER32.DLL
– 0x43e1e8: EnumWindows
– 0x43e1ec: GetWindowTextW
– 0x43e1f0: CharLowerW
– 0x43e1f4: GetActiveWindow
– 0x43e1f8: WinHelpW
[*] DLL: SHELL32.DLL
– 0x43e200: ShellExecuteExW
[*] DLL: WSOCK32.DLL
– 0x43e208: closesocket
– 0x43e20c: WSACleanup
– 0x43e210: WSAStartup
– 0x43e214: connect
– 0x43e218: socket
– 0x43e21c: inet_addr
– 0x43e220: gethostbyname
– 0x43e224: htons
– 0x43e228: bind
– 0x43e22c: ioctlsocket
– 0x43e230: select
– 0x43e234: __WSAFDIsSet
– 0x43e238: send
– 0x43e23c: sendto
– 0x43e240: recvfrom
– 0x43e244: recv
[*] DLL: NTDLL.DLL
p.p1 {margin: 0.0px 0.0px 0.0px 0.0px; font: 12.0px ‘Andale Mono’; color: #28fe14; background-color: #000000; background-color: rgba(0, 0, 0, 0.9)} span.s1 {font-variant-ligatures: no-common-ligatures; color: #34bbc8} span.s2 {font-variant-ligatures: no-common-ligatures}
– 0x43e24c: ZwQuerySystemInformation